Security in web applications is often seen as a developer's responsibility, but in reality, Quality Assurance plays a major role in protecting systems from vulnerabilities. One of the most common and dangerous security threats in web applications is SQL Injection. Even today, many production systems are exposed to this risk due to weak input validation or improper query handling.
Modern applications rely heavily on databases. User information, subscription data, billing records, orders, and reports are all stored in structured databases. If an attacker gains the ability to manipulate database queries, the impact can be severe. SQL Injection allows attackers to inject malicious SQL commands through user input fields and alter how the database behaves.
This blog explains what SQL Injection is, why it is dangerous, and how a QA engineer can actively help secure the system by identifying vulnerabilities before release.
Understanding SQL Injection
SQL Injection occurs when an application directly uses user input in SQL queries without proper validation or sanitization. When this happens, attackers can modify the structure of the query by inserting SQL commands.
For example, during login, the application checks the email and password against database records. If input validation is weak, an attacker can enter specially crafted values that manipulate the WHERE condition of the query, potentially bypassing authentication.
In more advanced attacks, malicious users may extract complete tables, modify records, or delete critical data.
Business Risks of SQL Injection
The business impact of SQL Injection can be massive. Some possible risks include:
- Unauthorized access to user accounts
- Leakage of customer personal information
- Exposure of payment and billing data
- Data corruption or deletion
- Legal penalties due to data protection violations
For subscription-based platforms, this could mean exposing thousands of active subscribers' data. In e-commerce systems, order and payment records may be compromised. Beyond financial loss, brand reputation and customer trust can suffer long-term damage.
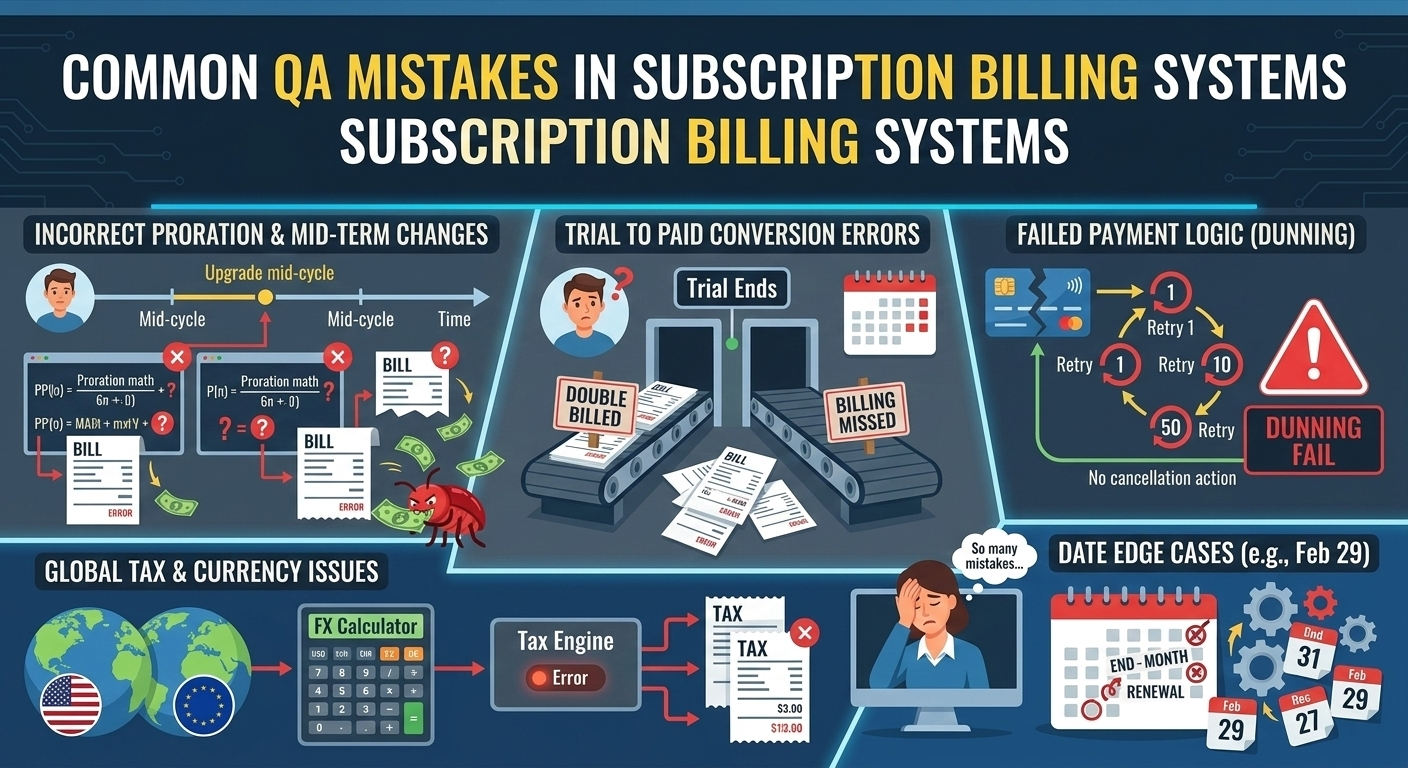
Common QA Mistakes in Security Testing
- Testing only positive scenarios: QA often verifies that forms work correctly with valid inputs but does not test malicious or unexpected inputs.
- Ignoring special characters: Input fields should be tested with quotes, semicolons, and SQL keywords to verify system behavior.
- Not verifying backend responses: Sometimes the UI shows a generic error, but backend APIs expose raw SQL error messages.
- Skipping API testing: Security testing should not be limited to the frontend. APIs must also be tested with modified payloads.
How QA Can Proactively Test for SQL Injection
QA engineers can follow a structured approach:
- Test login forms with unexpected inputs and observe system behavior.
- Modify URL parameters and check whether unauthorized data is returned.
- Test search boxes and filters with special characters.
- Use API tools to manipulate request payloads.
- Verify that error messages do not expose database-level details.
Security testing does not require advanced hacking skills. A careful and curious mindset is enough to identify most basic vulnerabilities.
Real Testing Scenario
During one testing cycle, while verifying authentication flows, negative testing was performed on the login form. The application correctly rejected invalid credentials, but it exposed a detailed database error message in response to certain special character inputs.
Although unauthorized access was not granted, the exposed error provided insight into the database structure. This was reported as a high-severity security issue. The development team implemented proper error handling and ensured parameterized queries were used consistently across the module.
This small finding significantly improved the overall security posture of the application.
Best Practices for Secure Systems
- Always use parameterized queries or prepared statements.
- Implement strong input validation at both frontend and backend.
- Avoid exposing detailed system errors to users.
- Conduct regular security testing as part of regression cycles.
- Include security scenarios in test cases from day one.
QA teams should collaborate closely with developers to ensure secure coding standards are followed.
Conclusion
SQL Injection remains one of the most critical web security vulnerabilities. While developers are responsible for implementing secure code, QA engineers act as the final checkpoint before production release.
By incorporating security-focused testing strategies into regular QA processes, teams can identify vulnerabilities early and prevent serious data breaches. Quality Assurance is not only about validating features - it is also about protecting the system, the data, and the business.